AI Career Growth Database Development Information Security Linux Microsoft Networking Tools
Tag: networking
-
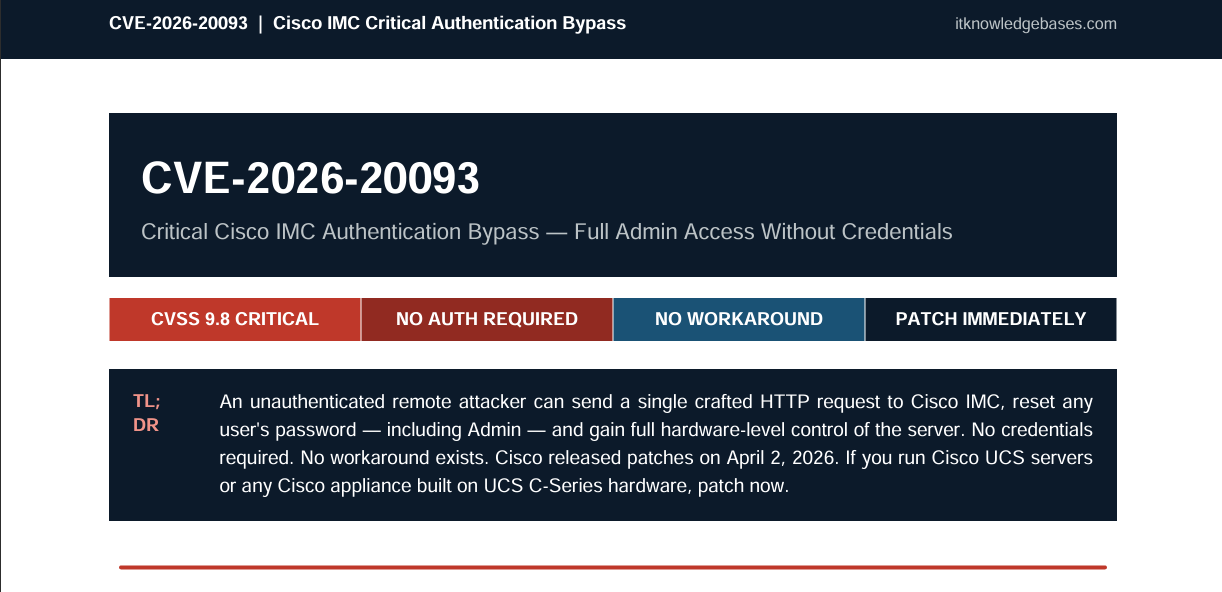
TL;DR CVE-2026-20093 is a critical authentication bypass vulnerability in Cisco’s Integrated Management Controller (IMC), carrying a CVSS score of 9.8 out of 10. An unauthenticated, remote attacker can exploit it by sending a single crafted HTTP request to reset the password of any user on the system — including the Admin account — and gain…
-
Executive Summary (For Management) Your organization’s firewall is only as secure as the system managing it. CVE-2026-20131 is a remote code execution (RCE) vulnerability in Cisco Secure Firewall Management Center (FMC), the central platform many organizations use to manage and coordinate their entire Cisco firewall estate. Abstract This is not a theoretical risk. It is…
-
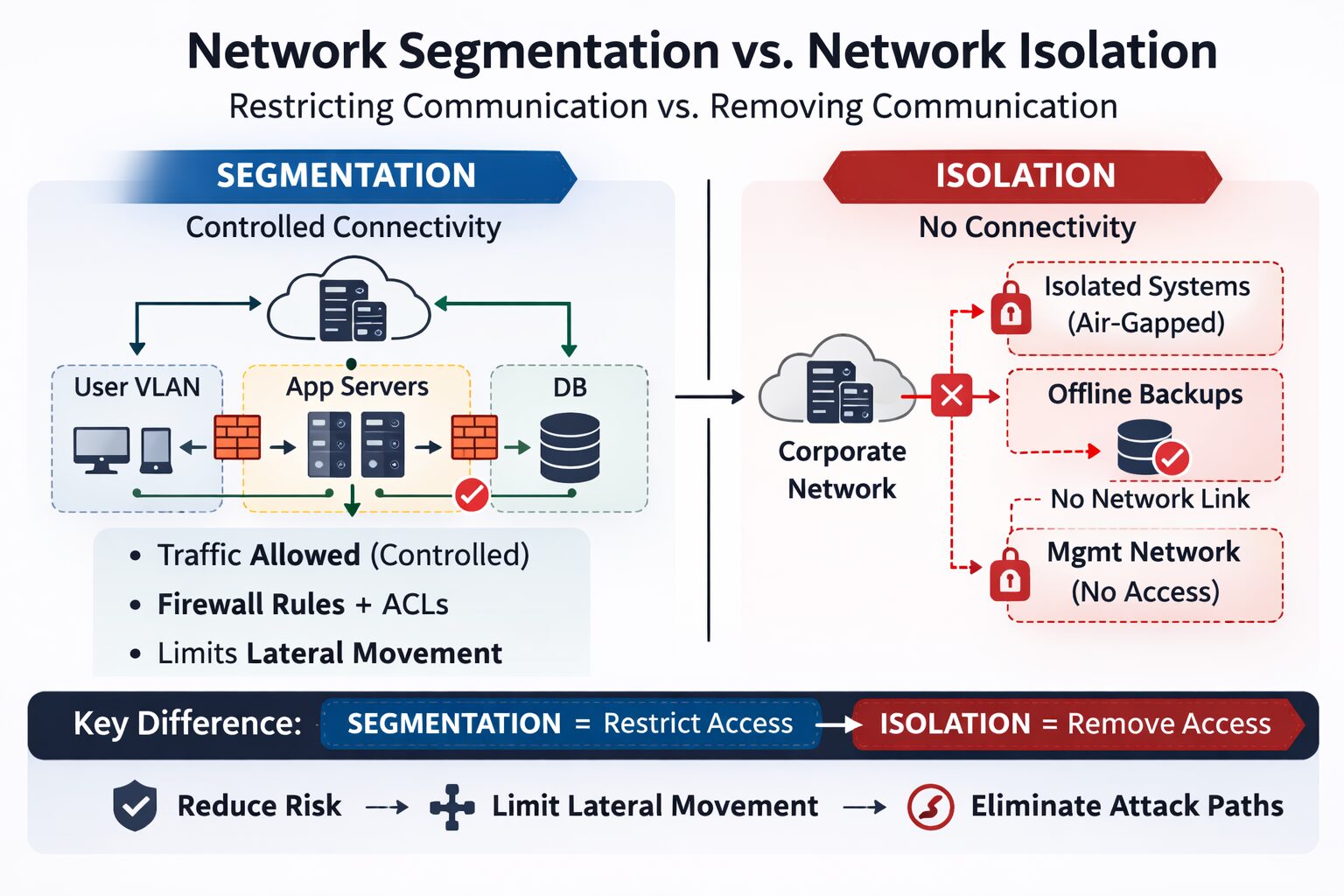
Network segmentation and network isolation are foundational concepts in secure network architecture. They’re often discussed together because both reduce risk, but they are not interchangeable and serve very different purposes in a security strategy. This matters for technical professionals who design, assess, or secure enterprise networks. Misunderstanding the distinction can lead to poor architecture decisions,…
-
Unsure which network switch to choose? Discover the key differences between unmanaged and managed switches to find the perfect fit for your network needs.
-
Safeguard sensitive hospital data with powerful firewalls. Discover how these crucial digital gatekeepers protect your network from threats and ensure patient privacy.
-
Master Linux network monitoring with our expert guide! Explore top tools to track & analyze network traffic (OSI layers 2-4). Boost performance & security now.