AI Career Growth Database Development Information Security Linux Microsoft Networking Tools
-
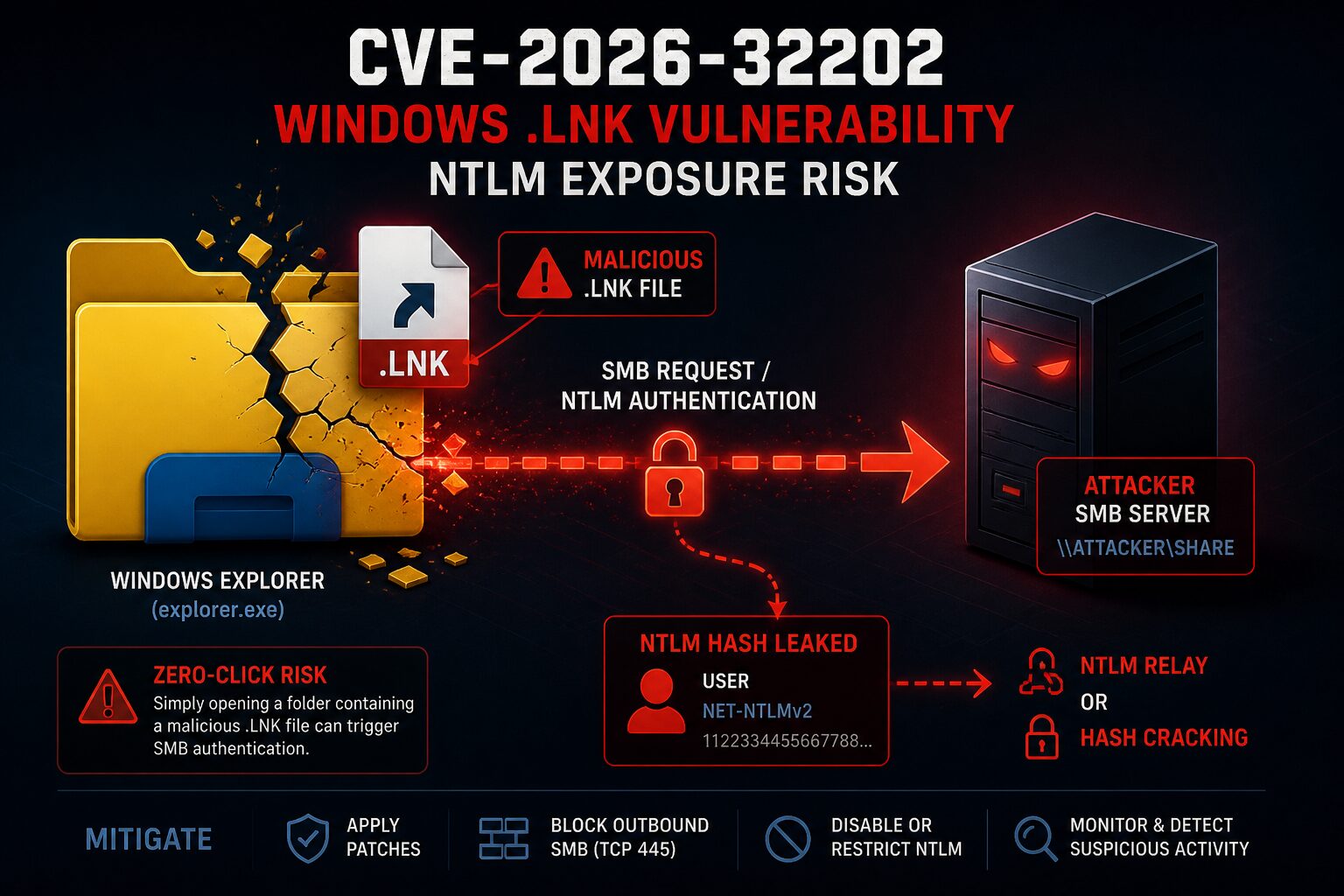
CVE-2026-32202 is a Windows Shell spoofing vulnerability involving protection mechanism failure in Microsoft Windows. NVD lists it as CVSS 4.3 Medium, but that score understates the operational risk — CISA has added it to the Known Exploited Vulnerabilities catalog, which in practice overrides the severity label for patching prioritization purposes. The core issue is that…
-
By now, you’ve heard of “Vibe Coding” or you wouldn’t be reading this. In a nutshell, it’s asking an AI to develop code for you. It started out harmless enough with one shot games that were pretty incredible to generate and play. The problem is that it evolved. Now, you have enterprises doing the same…
-
Most organizations treat IT like a utility—like the plumbing. You only notice it when it leaks. But in the modern enterprise, IT isn’t the plumbing; it’s the central nervous system. If you want to move from being a “tech person” to a strategic leader, you have to master COBIT (Control Objectives for Information and Related…
-
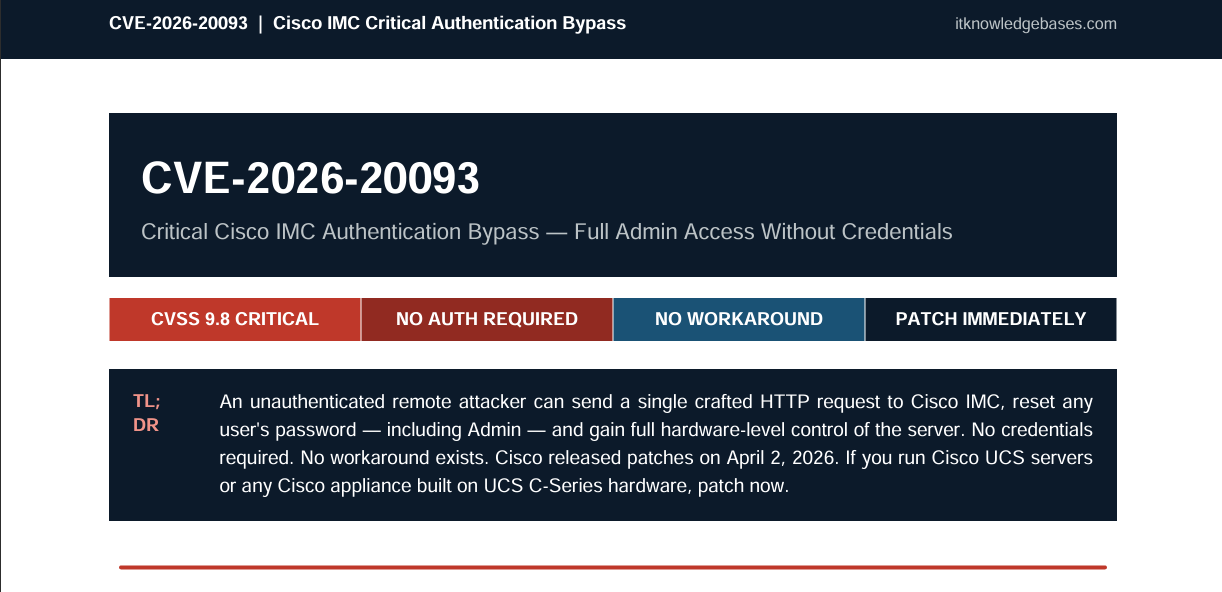
TL;DR CVE-2026-20093 is a critical authentication bypass vulnerability in Cisco’s Integrated Management Controller (IMC), carrying a CVSS score of 9.8 out of 10. An unauthenticated, remote attacker can exploit it by sending a single crafted HTTP request to reset the password of any user on the system — including the Admin account — and gain…
-
Executive Summary (For Management) Your organization’s firewall is only as secure as the system managing it. CVE-2026-20131 is a remote code execution (RCE) vulnerability in Cisco Secure Firewall Management Center (FMC), the central platform many organizations use to manage and coordinate their entire Cisco firewall estate. Abstract This is not a theoretical risk. It is…
-
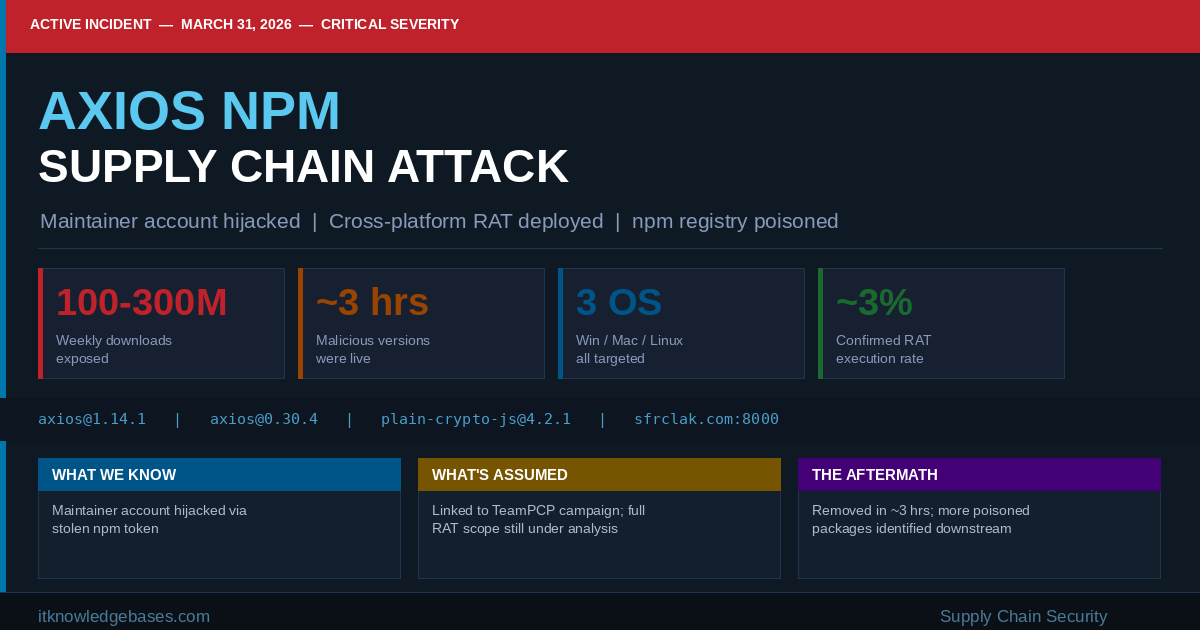
⚠ Active Incident Published: March 31, 2026 Category: Supply Chain Security Severity: Critical 🚨 Immediate Action Required If your environment ran npm install on axios between 00:21 UTC and 03:29 UTC on March 31, 2026, you may have deployed a Remote Access Trojan. Treat affected systems as fully compromised — do not attempt to clean…
-
Your employees are already using AI tools. ChatGPT, Microsoft Copilot, Google Gemini, Claude — they’re in your inbox, your documents, your customer support workflows, and your development pipelines. Most of them got there without a single security question being asked. This post introduces the AI Vendor Security Questionnaire for Business — a 40-question assessment built…
-
Most people assume that if they’re not doing anything wrong, they have nothing to worry about. That thinking made sense twenty years ago. It doesn’t anymore. Right now, foreign governments, shady data brokers, and surveillance-based apps are quietly building detailed profiles on ordinary Americans your location history, your health habits, who you call, what you…
-
Download Full Write-Up Here ⚠ CRITICAL — Active Exploitation This vulnerability is currently being exploited in the wild. The Cybersecurity and Infrastructure Security Agency (CISA) has added it to the Known Exploited Vulnerabilities (KEV) catalog with a required remediation deadline of March 10, 2026 for federal agencies.Action Required: Update affected browsers immediately and ensure systems…
-
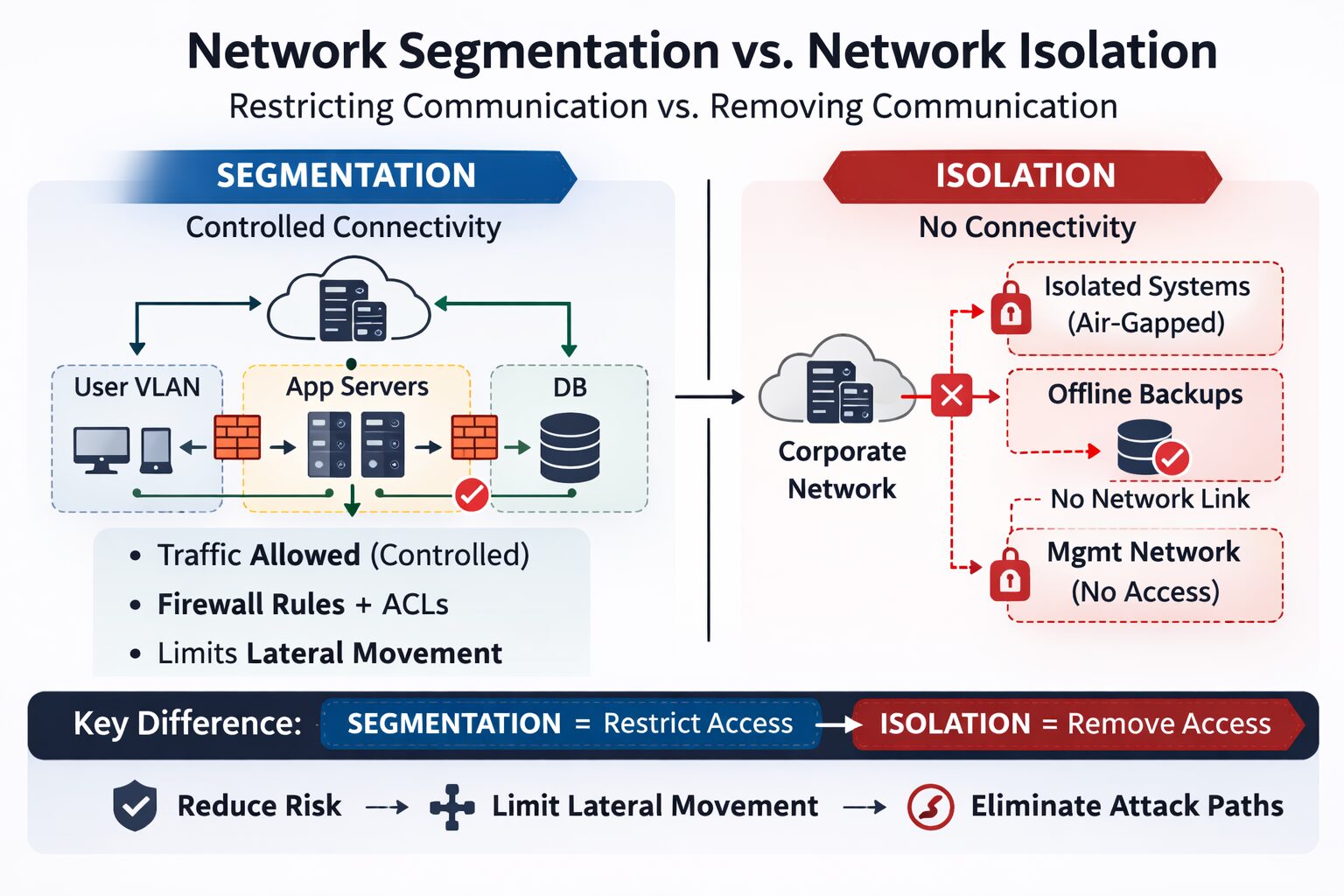
Network segmentation and network isolation are foundational concepts in secure network architecture. They’re often discussed together because both reduce risk, but they are not interchangeable and serve very different purposes in a security strategy. This matters for technical professionals who design, assess, or secure enterprise networks. Misunderstanding the distinction can lead to poor architecture decisions,…