AI Career Growth Database Development Information Security Linux Microsoft Networking Tools
Category: Tools
-
By now, you’ve heard of “Vibe Coding” or you wouldn’t be reading this. In a nutshell, it’s asking an AI to develop code for you. It started out harmless enough with one shot games that were pretty incredible to generate and play. The problem is that it evolved. Now, you have enterprises doing the same…
-
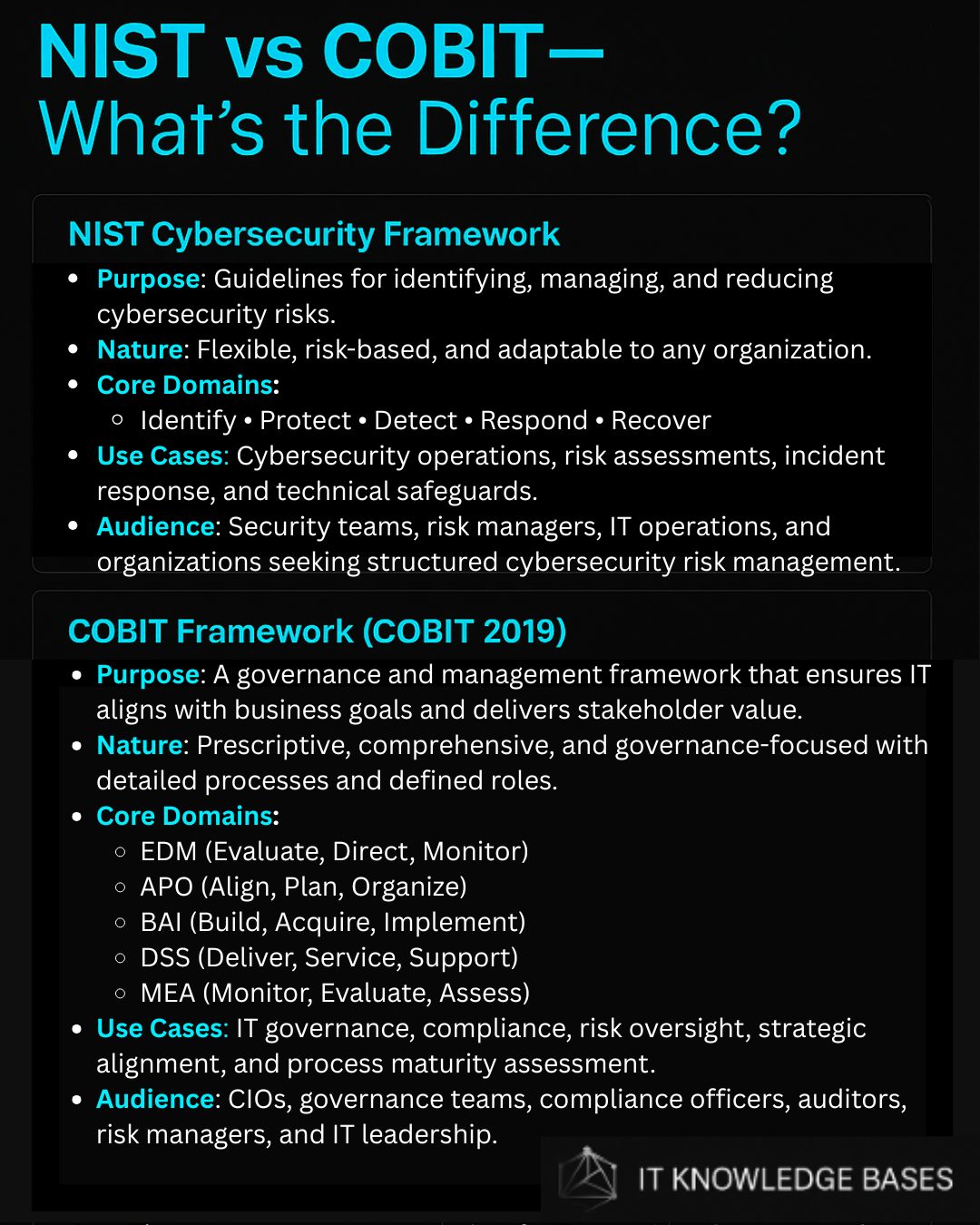
Most organizations treat IT like a utility—like the plumbing. You only notice it when it leaks. But in the modern enterprise, IT isn’t the plumbing; it’s the central nervous system. If you want to move from being a “tech person” to a strategic leader, you have to master COBIT (Control Objectives for Information and Related…
-
Download Full Write-Up Here ⚠ CRITICAL — Active Exploitation This vulnerability is currently being exploited in the wild. The Cybersecurity and Infrastructure Security Agency (CISA) has added it to the Known Exploited Vulnerabilities (KEV) catalog with a required remediation deadline of March 10, 2026 for federal agencies.Action Required: Update affected browsers immediately and ensure systems…
-
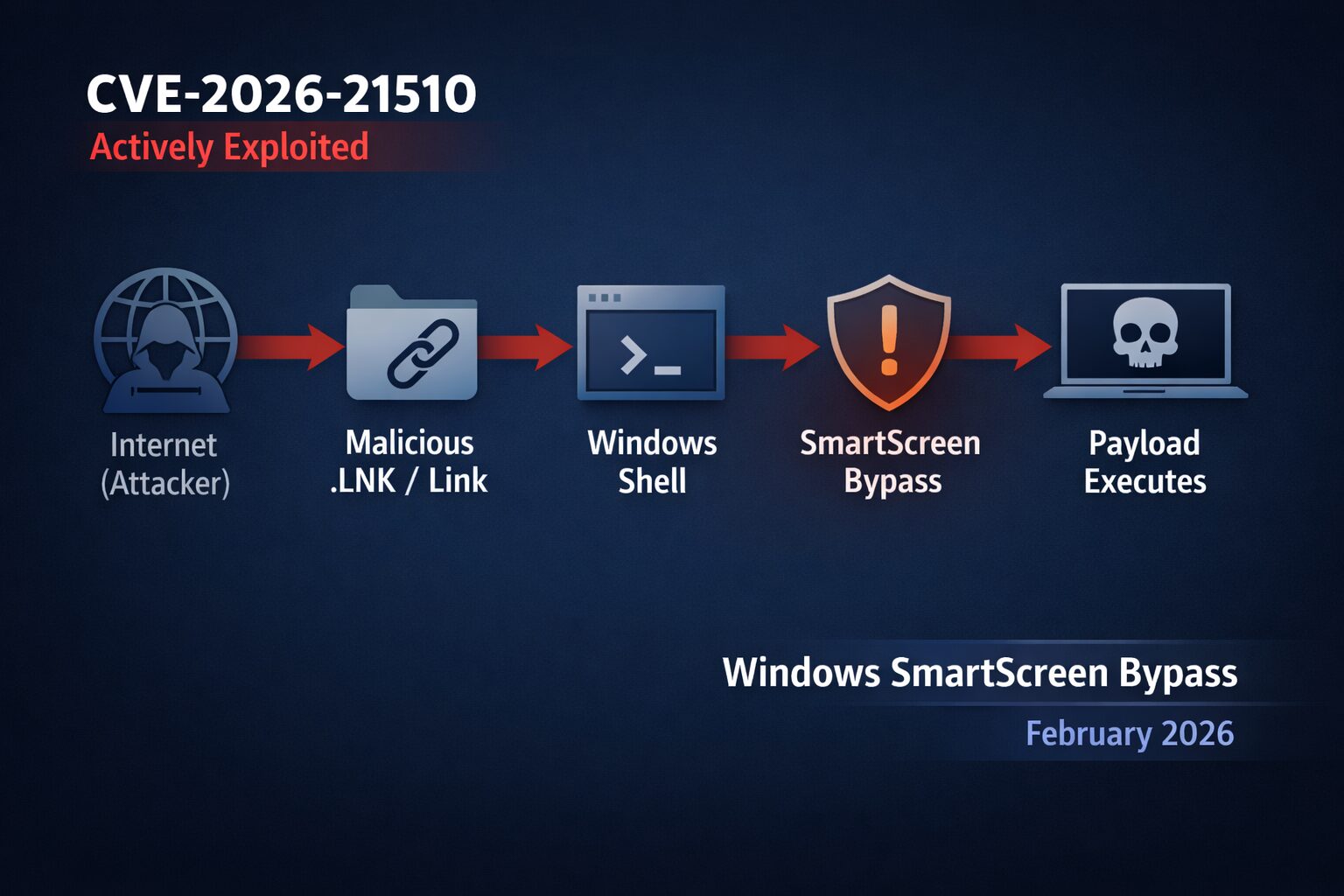
Microsoft’s February 2026 Patch Tuesday introduced a significant zero-day vulnerability tracked as CVE-2026-21510, which was both publicly disclosed before a patch and actively exploited in the wild. 1. Summary: What Is CVE-2026-21510? CVE-2026-21510 is a Windows Shell Security Feature Bypass vulnerability with a CVSS v3.1 base score of 8.8. It affects Microsoft Windows operating systems…
-
Summary: Why This Matters CVE-2026-21858 is a critical unauthenticated remote code execution (RCE) vulnerability affecting self-hosted n8n, a popular workflow automation platform used to orchestrate API calls, cloud services, and internal systems. If an exposed n8n instance is vulnerable, an attacker can fully compromise it without credentials, extract automation secrets, and pivot into connected infrastructure.…
-
Table of Contents 1. Overview NIST CSF and COBIT 2019 are two widely referenced frameworks in cybersecurity and IT governance. Many IT professionals understand pieces of each but struggle with how they differ in practice. One is focused on cybersecurity risk; the other is focused on governance and accountability. This blog breaks down their roles,…
-
Learn how to spot phishing emails as attacks grow more sophisticated. See how scammers use disguises and generative AI to make fake emails look real.
-
Is your risk matrix failing? Learn how to turn Impact × Likelihood into actionable SLAs, owners, and measurable progress that drives real fixes.
-
Start your Raspberry Pi 5 journey with the CanaKit Starter Kit PRO! This comprehensive package has all you need to unleash your creativity. Shop now!
-
Unlock AI’s power for IT! Boost system management, enhance security & drive efficiency. A must-read guide for IT professionals. Learn best practices.