TL;DR
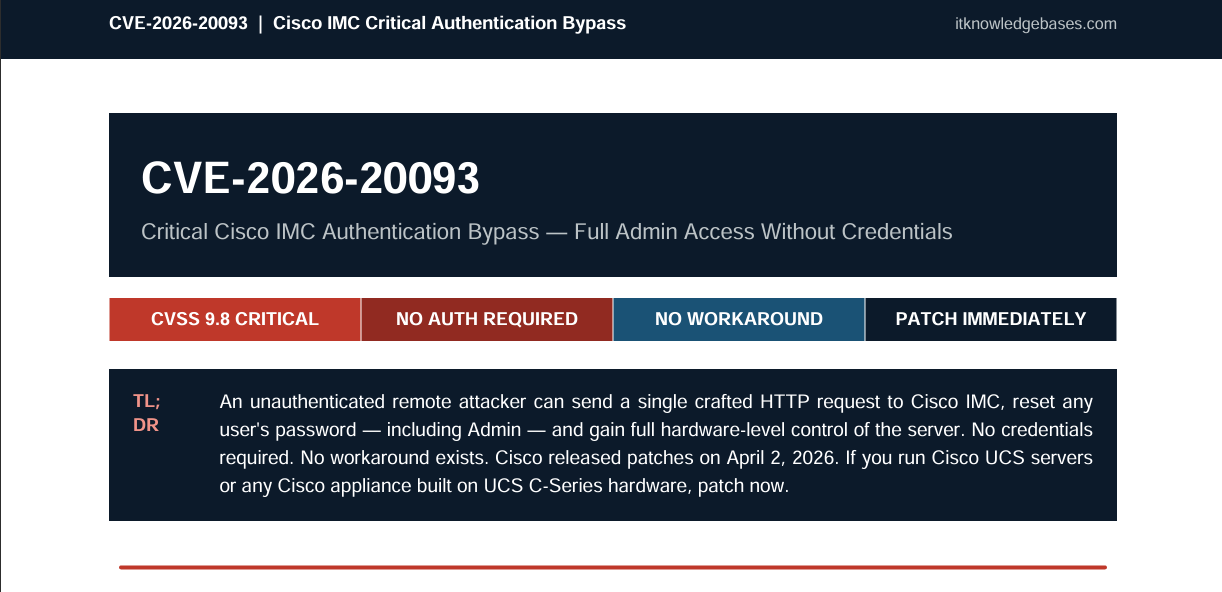
CVE-2026-20093 is a critical authentication bypass vulnerability in Cisco’s Integrated Management Controller (IMC), carrying a CVSS score of 9.8 out of 10. An unauthenticated, remote attacker can exploit it by sending a single crafted HTTP request to reset the password of any user on the system — including the Admin account — and gain full hardware-level control of the server. Cisco patched this on April 2, 2026. If you run Cisco UCS servers or any Cisco appliance built on UCS C-Series hardware, this is a drop-everything patch.
What Is CVE-2026-20093?
CVE-2026-20093 is a critical authentication bypass flaw residing in the change password functionality of Cisco’s Integrated Management Controller (IMC) software. Cisco IMC is a baseboard management controller (BMC) — a dedicated hardware chip embedded in Cisco UCS servers that gives administrators out-of-band remote management capabilities: power cycling, BIOS configuration, KVM access, and virtual media mounting, all independently of whatever operating system is running on the server.
The vulnerability was discovered and responsibly disclosed to Cisco’s Product Security Incident Response Team (PSIRT) by security researcher “jyh.” Cisco published its advisory on April 2, 2026, alongside patches for nine other IMC vulnerabilities.
The root cause is improper input validation (CWE-20) in the IMC’s handling of password change requests. The system’s XML API endpoint processes password modification requests before fully validating whether the source has an authenticated, authorized session — a classic authentication logic flaw. By structuring an HTTP POST request in a specific way targeting the configConfMo method against the aaaUser object class, an attacker can cause the backend to accept and commit a new password to the system database without ever proving their identity.
Why This Is Especially Dangerous: The BMC Attack Surface
Most vulnerabilities live at the operating system or application layer. CVE-2026-20093 is different — it targets the Baseboard Management Controller, which operates below the OS layer. This has profound security implications:
- EDR and endpoint security tools are blind to it. Traditional Endpoint Detection and Response solutions run inside the OS. A compromised IMC is invisible to them.
- SIEM detections may miss it. Because IMC activity is out-of-band, it doesn’t pass through normal OS log pipelines.
- OS-level hardening doesn’t protect you. Firewalls, SELinux policies, and host-based controls all live above the IMC layer.
- Persistence survives OS reinstalls. An attacker with IMC admin access can mount malicious virtual media and compromise the server even after a complete OS wipe.
Expert view: “An authentication bypass at this level effectively hands attackers full administrative control over the hardware itself, meaning traditional security controls — EDR, SIEM detections, even OS-level hardening — become largely irrelevant once exploited.” — Ensar Seker, CISO, SOCRadar
This is what makes CVE-2026-20093 a Tier-0 threat. It doesn’t matter how well-hardened your Linux installation is if an attacker can reset the IMC admin password, log in, and reimage your server from scratch.
CVSS 3.1 Breakdown
| Metric | Value |
|---|---|
| CVSS Score | 9.8 / Critical |
| Attack Vector | Network |
| Attack Complexity | Low |
| Privileges Required | None |
| User Interaction | None |
| Confidentiality Impact | High |
| Integrity Impact | High |
| Availability Impact | High |
| CWE | CWE-20 (Improper Input Validation) |
The score of 9.8 reflects a worst-case exploitation scenario: no credentials, no user interaction, exploitable remotely, low complexity. In practice, if your IMC interface is reachable from an attacker — even on an internal network — this is effectively a full compromise waiting to happen.
Affected Products
CVE-2026-20093 affects the following Cisco enterprise hardware regardless of device configuration:
Directly Affected Server Platforms
- Cisco 5000 Series Enterprise Network Compute Systems (ENCS)
- Cisco Catalyst 8300 Series Edge uCPE platforms
- Cisco UCS C-Series M5 and M6 Rack Servers (standalone mode)
- Cisco UCS E-Series M3 and M6 Servers
- Cisco UCS S-Series Storage Servers
Affected Cisco Appliances (if IMC UI is exposed)
- Application Policy Infrastructure Controller (APIC) Servers
- Catalyst Center Appliances
- Cyber Vision Center Appliances
- Secure Firewall Management Center Appliances
- Secure Network Analytics Appliances
- Malware Analytics Appliances
- And dozens of other Cisco product lines built on UCS C-Series hardware
Not Affected
- UCS B-Series Blade Servers
- UCS C-Series M7 and M8 Rack Servers in standalone mode
Fixed Firmware Versions
| Product | Fixed Version |
|---|---|
| UCS C-Series M5/M6 (standalone) | 4.3(2.260007), 4.3(6.260017), or 6.0(1.250174) |
| 5000 Series ENCS | NFVIS 4.15.5 |
| Catalyst 8300 uCPE | NFVIS 4.18.3 |
| UCS E-Series | Consult the official Cisco advisory for platform-specific versions |
There are no workarounds. Cisco has confirmed that no configuration change can mitigate this vulnerability without fully disabling the IMC management interface. A firmware update is the only fix.
How Exploitation Works
Exploitation is straightforward and requires no specialized tooling:
- Reconnaissance: The attacker identifies an IMC web interface or XML API port reachable over the network — commonly TCP port 443 or 80.
- Crafted request: A specially structured HTTP POST is sent to the XML API endpoint targeting the
configConfMomethod against theaaaUsermanaged object class. - Auth bypass: The IMC processes the payload before fully validating the session context. The backend commits the attacker’s chosen password with no session token required.
- Admin login: The attacker logs into the IMC using the newly set Admin password.
- Total hardware control: The attacker can now reboot the server, modify BIOS settings, disable Secure Boot, mount malicious virtual media, install persistent backdoors, or pivot laterally to other systems on the management network.
The full attack chain from initial request to admin access takes seconds. Automation into a scanner or exploit kit is trivial.
Is There Active Exploitation?
As of the Cisco advisory release on April 2, 2026, no public exploit code exists and no active exploitation in the wild has been confirmed. However, the risk of imminent weaponization is high:
- CVE-2026-20131 in Cisco Secure Firewall Management Center was exploited by the Interlock ransomware gang in zero-day attacks and added to CISA’s Known Exploited Vulnerabilities catalog — demonstrating how quickly adjacent Cisco flaws get weaponized.
- Research from DeepStrike found that in 2025, attackers exploited 28% of vulnerabilities within one day of CVE disclosure.
- BMC-level vulnerabilities are prime targets for APT groups and ransomware operators due to the deep, OS-independent persistence they enable.
The window between “no known exploits” and “actively weaponized” is narrowing every year. Treat this as urgent regardless of the current exploitation status.
Immediate Action Plan
1. Inventory Your Exposure Right Now
Run a scan or audit of your environment to identify every device running Cisco IMC — servers, APIC nodes, Firewall Management Centers, and other Cisco appliances built on UCS C-Series hardware. Check whether their IMC interfaces are accessible from outside your dedicated management VLAN.
2. Patch Immediately
Apply the firmware updates from the Fixed Firmware Versions table above. Prioritize any IMC interface reachable from untrusted or semi-trusted segments.
3. Audit IMC User Accounts Before Patching
Because exploitation leaves few traces in standard OS logs, manually review all IMC user accounts right now for rogue accounts, unexpected admin password changes, or accounts with unusual creation timestamps.
4. Isolate All IMC Interfaces to a Dedicated Management VLAN
BMC interfaces must never be reachable from general corporate networks or the public internet. Place all IMC interfaces on a dedicated, heavily firewalled management VLAN with strict ACLs — non-negotiable regardless of patch status.
5. Force All IMC Access Through Hardened Jump Hosts
Require administrators to authenticate through a hardened jump host with multi-factor authentication (MFA) and session logging before accessing any IMC interface. Block direct routing to the management network at the perimeter.
6. Enable SIEM Alerting for IMC Log Events
Configure alerts for: password change events not correlated with a maintenance window; unauthenticated POST requests to password-change URIs; management traffic from IPs outside designated admin subnets; IMC login events from unexpected source IPs.
Broader Context: Why BMC Security Is a Blind Spot
CVE-2026-20093 is part of a growing pattern. Baseboard management controllers — including Cisco IMC, Dell iDRAC, HPE iLO, and the open-standard OpenBMC — are increasingly targeted precisely because they operate outside the reach of conventional security tooling. High-profile incidents like the 2020 supply chain attacks on server firmware demonstrated that nation-state actors are actively interested in sub-OS persistence.
Despite this, BMC interfaces in many enterprise environments are insufficiently segmented, sometimes reachable from general corporate networks, and rarely included in vulnerability scanning programs. CVE-2026-20093 is a reminder that out-of-band management is an attack surface that demands the same rigorous hardening as any perimeter-facing system — arguably more so, given what’s at stake.
Key Takeaways
- CVE-2026-20093 is a CVSS 9.8 authentication bypass in Cisco IMC, disclosed April 2, 2026.
- An unauthenticated attacker can reset any user’s password — including Admin — with a single crafted HTTP request.
- It affects Cisco UCS C-Series M5/M6 servers in standalone mode, E-Series servers, ENCS, Catalyst 8300 uCPE, and dozens of Cisco appliances built on UCS hardware.
- The IMC operates below the OS layer, meaning EDR, SIEM, and OS hardening offer no protection against exploitation.
- No workarounds exist — the only fix is a firmware update.
- No active exploitation confirmed as of April 2, 2026, but exploitation complexity is extremely low and attacker interest is extremely high.
- Patch, isolate IMC interfaces to a management VLAN, audit accounts, and implement jump host access controls immediately.
Frequently Asked Questions
What is CVE-2026-20093?
CVE-2026-20093 is a critical (CVSS 9.8) authentication bypass vulnerability in Cisco’s Integrated Management Controller (IMC). It allows an unauthenticated remote attacker to reset any user’s password — including the Admin account — by sending a single crafted HTTP request, granting full hardware-level control of the affected server.
Which Cisco products are affected?
Affected products include Cisco UCS C-Series M5 and M6 Rack Servers in standalone mode, UCS E-Series M3 and M6, 5000 Series ENCS, Catalyst 8300 Series Edge uCPE, and dozens of Cisco appliances built on UCS C-Series hardware — including APIC Servers, Catalyst Center Appliances, and Secure Firewall Management Center Appliances.
Is there a workaround for CVE-2026-20093?
No. Cisco has confirmed there are no configuration workarounds that mitigate this vulnerability without disabling the IMC management interface entirely. The only fix is applying the firmware updates released April 2, 2026.
Is CVE-2026-20093 being actively exploited?
As of April 2, 2026, no active exploitation has been confirmed. However, exploitation complexity is extremely low and similar Cisco vulnerabilities have been weaponized within days of disclosure. Treat this as an immediate priority.
Enjoy Articles like this? Subscribe below and check out more articles:
CVE-2026-20131: Critical Cisco FMC Remote Code Execution — What You Need to Know
References
- Cisco Official Security Advisory
- BleepingComputer — Critical Cisco IMC Auth Bypass Gives Attackers Admin Access
- Help Net Security — Cisco IMC Vulnerability CVE-2026-20093
- The Hacker News — Cisco Patches 9.8 CVSS IMC and SSM Flaws
- SOCRadar — Technical Analysis of CVE-2026-20093
- CISA Known Exploited Vulnerabilities Catalog
- NVD Entry: CVE-2026-20093
Leave a Reply
You must be logged in to post a comment.