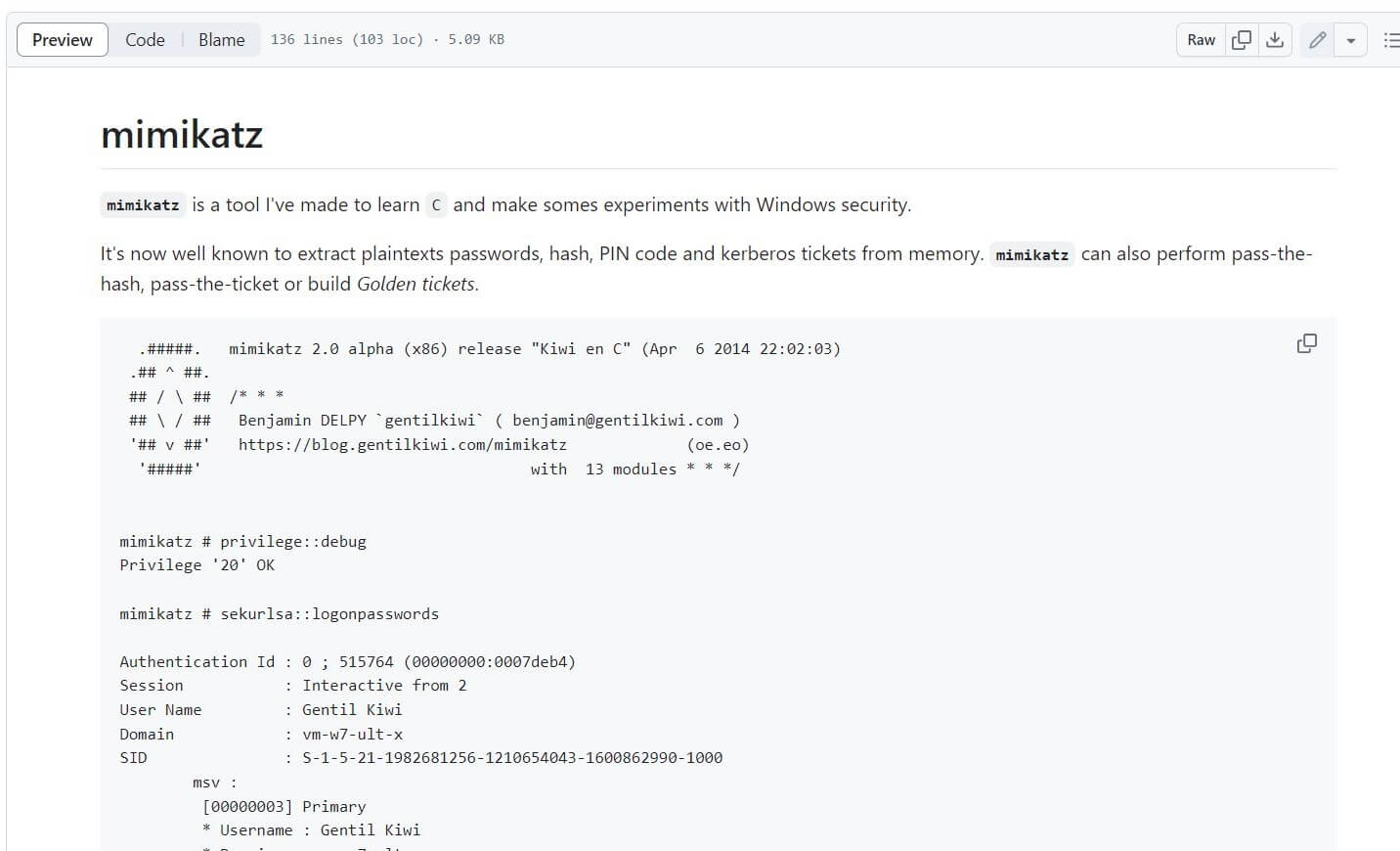
Originally Developed by Benjamin Delpy. Mimikatz is an open-source program that can extract passwords, PINs, hashes, and Kerberos tickets from Windows memory. It can be used as an attack tool against Windows clients to steal credentials, escalate privileges, and gain unauthorized access to restricted areas of a system.
The most well-known portion of Mimikatz is the ability to extract plain-text passwords. Some people might say “so what, im on the defensive side? why do i care what this tool is? in simple terms it’s easy to use and popular.
Who Uses Mimikatz
Mimikatz is not a super confidential tool only used by the top hackers. it is popular because it is simple and easy to use. While this is not an exhaustive list you will get the point. These groups use Mimikatz for activities like credential dumping, privilege escalation, and lateral movement within networks. Here are some notable APT groups known to use Mimikatz:
- APT28 (Fancy Bear / Sofacy / Sednit): This Russian cyber espionage group has been known to use Mimikatz in their operations, particularly to extract credentials and maintain persistence in targeted networks.
- APT29 (Cozy Bear / The Dukes / The APT29 Group): Another Russian group, APT29 employs Mimikatz for similar purposes, including credential harvesting and maintaining access to compromised networks.
- Lazarus Group: This North Korean group, notorious for its cyber-attacks and financial theft, uses Mimikatz among other tools to facilitate their operations and move laterally within compromised environments.
- DarkHydrus: This group, known for targeting organizations in the Middle East, has been observed using Mimikatz to extract credentials and expand their access within networks.
- MuddyWater: This Iranian group is known to use Mimikatz for credential dumping and privilege escalation as part of their cyber-espionage activities.
What are the most common Mimikatz attack vectors?
- Weak and Compromised Credentials: Mimikatz exploits weak passwords, pass-the-hash, and pass-the-ticket techniques to steal credentials and gain unauthorized access.
- Endpoint Vulnerabilities: Unpatched or outdated systems, particularly Windows 7 or earlier, can be exploited by Mimikatz to extract sensitive information.
- Privilege Escalation: Gaining elevated privileges allows attackers to activate WDigest, bypass LSA protection, and run Mimikatz attacks successfully.
- RAM-based Attacks: Mimikatz can extract credentials from system memory (RAM) without writing to disk, making it difficult to detect.
How to Prevent MimiKatz
Now to start digging into how to make this attack a bit more difficult. here are some quick tips on how to do some decent mitigation against this tool.
- Implement Strong Authentication: Use multi-factor authentication (MFA) and enforce regular password changes to reduce the effectiveness of credential theft.
- Keep Systems and Software Up-to-Date: Ensure all Windows systems and software are patched and updated to mitigate known vulnerabilities.
- Disable WDigest: Disable WDigest by default and consider implementing alternative authentication mechanisms.
- Enable LSA Protection: Enable LSA protection to limit access to sensitive data and make it more difficult for attackers to run Mimikatz attacks.
To view the code version 2.0 it is available to view at https://github.com/gentilkiwi/mimikatz
Enjoy reading articles about Security?
Check out our Security Category!
Leave a Reply
You must be logged in to post a comment.